Automotive Software Development Services: What to Look For in a Partner
April 27
Published
Nazar Verhun
CEO & Lead Designer at MyPlanet Design

Most supplier qualification failures we’ve witnessed don’t happen because the engineering was bad. They happen because a team that builds excellent enterprise software walks into an OEM audit assuming their existing QMS translates to automotive. It doesn’t.
The gap between general software competency and automotive-grade certification readiness is where projects die — quietly, expensively, and usually around ASPICE Level 2 assessments when the acquirer realizes their vendor can’t produce traceable work products. Choosing the right automotive software development services partner isn’t about scanning portfolios for dashboard screenshots or counting embedded engineers on LinkedIn. It’s about verifying whether a vendor’s process architecture can survive the specific documentary and procedural scrutiny that ISO 26262 ASIL classifications and OEM-specific audit frameworks demand.
We’ve sat through enough supplier selection rounds to spot the pattern: teams that pass technical interviews but collapse under process evidence requests. The certification bar in 2026 has only gotten stricter, with updated ASPICE 4.0 model requirements reshaping how assessors evaluate software engineering practices across the supply chain.
What separates a competent development partner from a qualified one comes down to a handful of verifiable criteria — none of which appear on a typical RFP checklist.
Key Takeaways:
– General software development excellence does not equal automotive certification readiness — verify process maturity separately.
– Demand evidence of ASPICE Level 2+ assessment history before shortlisting any vendor.
– Evaluate traceability toolchains (requirements → code → test) as a non-negotiable gating criterion.
– Ask for OEM audit survival rates, not just client logos.
– ISO 26262 ASIL capability must match your specific product’s safety integrity level — not every vendor covers ASIL-C/D.
– Treat the ASPICE 4.0 model update as your baseline for 2026 evaluations, not the legacy 3.1 framework.
What Do Automotive Software Development Services Actually Include?

Automotive software development services span five distinct technical domains, each with its own toolchains, compliance requirements, and talent profiles. Treating them as a single category is how projects get scoped wrong before a line of code ships.
The Five Core Service Categories
1. Embedded ECU Software — Firmware running on electronic control units that manage powertrain, braking, and chassis systems. Built on AUTOSAR Classic (for legacy architectures) or AUTOSAR Adaptive (for high-performance compute platforms), typically written in MISRA-compliant C/C++ and deployed on real-time operating systems like QNX or VxWorks.
2. ADAS and Sensor Fusion Pipelines — Perception stacks processing data from lidar, radar, and camera arrays into actionable driving decisions. Heavy use of ROS 2, TensorRT, and CUDA-accelerated inference, with latency budgets measured in single-digit milliseconds.
3. Infotainment and HMI Systems — Driver-facing interfaces built on Android Automotive OS or Qt/QML frameworks. These touch UX design, voice interaction, and app ecosystem integration — closer to consumer software than anything else on this list.
4. OTA Update Infrastructure — Secure over-the-air platforms managing firmware distribution across vehicle fleets. Cloud-native architectures (typically AWS IoT or Azure IoT Hub) handling delta updates, rollback mechanisms, and campaign management for millions of endpoints.
5. V2X and Telematics Platforms — Vehicle-to-everything communication systems using SOME/IP, MQTT, or CAN-FD protocols to exchange data between vehicles, infrastructure, and cloud backends.
The scale involved is staggering. According to McKinsey’s 2022 Software-Defined Vehicle report, modern vehicles now run on over 100 million lines of code, and software is projected to represent 45% of a vehicle’s total value by 2030. That projection alone explains why OEMs in 2026 are restructuring entire procurement strategies around software competency rather than mechanical capability.
Why Safety Classification Changes Everything
Here’s where most partner evaluations collapse: applying a uniform compliance lens across all five categories.
ISO 26262 functional safety ratings range from QM (quality management — no specific safety obligations) through ASIL-A up to ASIL-D, the highest integrity level. Safety-critical ECU code managing braking or steering demands ASIL-B through ASIL-D certification. Infotainment HMI? Typically QM. Conflating these requirements produces two equally expensive mistakes — over-engineering a media player to safety-critical standards (burning budget and timeline) or under-certifying a brake controller to QM level (risking lives and recall liability).
ASPICE adds a process maturity dimension that’s orthogonal to safety. An OEM requiring ASPICE Level 2 doesn’t care whether your engineers are brilliant — they care whether your requirements traceability, change management, and verification workflows are documented and repeatable. We’ve seen technically excellent teams fail supplier audits because their Git workflow didn’t map to ASPICE’s process reference model. No amount of clean code compensates for missing bidirectional traceability between requirements and test cases.
What Requires Specialist Expertise — and What Doesn’t
So where should you actually draw the line during partner selection?
Not every piece of automotive and mobility software demands a team steeped in functional safety standards. A competent full-stack agency can handle API integrations, fleet management web dashboards, connected-car cloud backends, and companion mobile apps — the IT-adjacent layer above the vehicle’s embedded systems.
What demands domain-specific expertise: MISRA-C/C++ compliance, real-time OS scheduling with deterministic timing guarantees, Hardware-in-the-Loop (HiL) test infrastructure, and hardware-software co-design where firmware and silicon evolve in lockstep.
| Capability Area | Generalist Software Agency | MyPlanet Design |
|---|---|---|
| Connected car cloud backends & APIs | Strong — standard cloud engineering applies | Strong — full-stack cloud and web architecture expertise |
| HMI/UX design & infotainment UI | Moderate — lacks automotive UX context | Strong — design-driven development with automotive domain exposure |
| Embedded ECU / safety-critical firmware | Not equipped — no MISRA, RTOS, or HiL tooling | — (requires certified Tier-1 automotive specialist) |
| OTA platform architecture | Moderate — IoT patterns transfer partially | Strong — cloud-native architecture with DevOps capability |
That honest distinction matters more than any marketing claim. If your project lives in the cloud-to-cabin pipeline — telematics dashboards, OTA orchestration, companion apps — a full-stack digital partner with automotive context gets you to production faster than a pure-play embedded shop. If you’re writing brake controller firmware, you need a certified Tier-1 supplier. Full stop.
What Should You Verify Before Signing with an Automotive Software Development Partner?

Before contracting automotive software development services, verify five non-negotiable credentials: ASPICE Level 2+ assessment by an independent assessor, a documented ISO 26262 safety case from a prior project, a named Functional Safety Manager on the delivery team, hands-on AUTOSAR toolchain experience (Vector CANoe, ETAS INCA, or dSPACE), and a defined ISO/SAE 21434 cybersecurity methodology.
Miss even one, and you’re facing a failed supplier audit — or worse, a safety case that collapses under OEM scrutiny.
The SWE.2 Trap
Across multiple supplier qualification reviews, we’ve watched the same failure mode repeat. Vendors with strong enterprise or web portfolios consistently stall at ASPICE’s SWE.2 (Software Architectural Design) process area. Why? Their process documentation maps to agile sprint backlogs and Jira epics — not the formal bidirectional traceability matrices OEM auditors expect between requirements, architecture elements, and test cases.
This pattern isn’t random. Enterprise software teams optimize for shipping velocity; ASPICE optimizes for process evidence. The two mindsets produce fundamentally different artifacts.
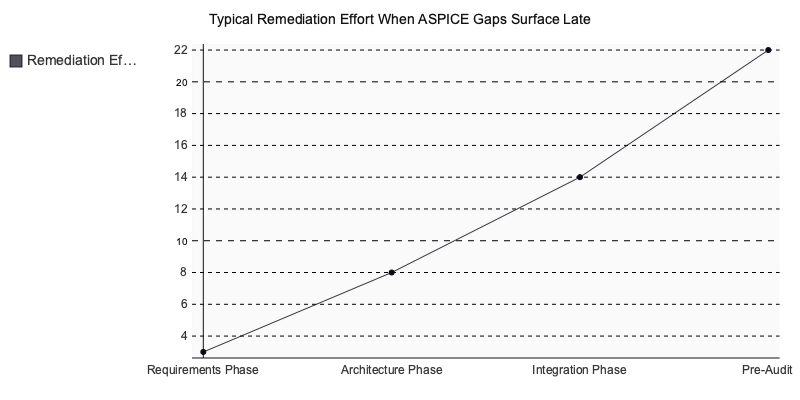
Remediation isn’t trivial either. Retrofitting SWE.2-compliant architectural documentation into an active project typically adds 8–14 weeks and pulls senior architects off feature delivery. In the qualification reviews we’ve supported, this rework consistently pushed budgets into six-figure territory before SOP readiness. For programs targeting a 2026 launch, that delay cascades into missed OEM milestones and erodes procurement confidence before a single release ships.
Five-Point Compliance Verification Checklist
- Request an independently issued ASPICE assessment report — self-declarations don’t survive OEM audits. The assessor must be intacs-certified.
- Ask for HARA output from a prior project. If the vendor can’t produce a Hazard Analysis and Risk Assessment, their ISO 26262 claim is theoretical.
- Verify tool qualification certificates for every safety-critical toolchain in the proposed stack. Unqualified tools invalidate safety arguments entirely.
- Confirm TARA experience per ISO/SAE 21434 through a concrete project example — not a slide deck. Cybersecurity process maturity is now a gate in most automotive & mobility programs.
- Check for a Development Interface Agreement template applied on prior OEM work. Its absence signals the vendor hasn’t navigated multi-party development coordination — a gap that compounds as technology complexity scales.
Skip any vendor that can’t clear items one through three — those are pass/fail gates, not negotiation points. Items four and five then separate genuinely capable partners from vendors whose process gaps will surface mid-program and destroy your schedule.
Automotive Software Development Services Vs. General Software Agencies: a Technical Comparison

The gap between a general software agency and a vendor qualified for automotive software development services isn’t a matter of degree — it’s structural. Different toolchains, different process models, different team compositions. Confusing the two costs projects six to twelve months of rework, typically discovered during the first OEM supplier audit.
Four Dimensions That Separate the Two
| Dimension | Automotive-Specialized Vendor | General Software Agency | MyPlanet Design |
|---|---|---|---|
| Toolchain | MATLAB/Simulink MBD, AUTOSAR BSW config (Vector DaVinci, ETAS INCA, dSPACE) | GitHub, CI/CD pipelines, cloud-native stacks | Cloud-native stacks, CI/CD, Figma-to-code design pipelines |
| Testing | HIL/SIL test benches, ISO 26262 fault injection | Automated unit/integration testing, browser and device testing | Automated unit/integration, device-lab mobile testing |
| Development Model | V-model with mandatory safety review gates | Two-week agile sprints | Agile with structured review gates where compliance demands it |
| Team Structure | Functional Safety Engineer, Safety Manager, ASPICE assessor | Product manager, full-stack developers, QA | UX researchers, product designers, full-stack engineers, QA |
That table isn’t academic. Tier-1 suppliers like Bosch and Continental contractually require ASPICE Level 2+ from every software vendor in their supply chain. If your partner can’t demonstrate SWE.1 through SWE.6 process compliance, they won’t pass supplier qualification — regardless of how clean the code is.
Why This Market Commands a Premium
According to Statista’s 2024 automotive software market analysis, the global market was valued at $22.6 billion in 2023 and is projected to exceed $43 billion by 2030. That growth isn’t driven by volume alone — it reflects the regulatory and tooling complexity that separates this domain from general enterprise development. Specialized vendors command 30–50% rate premiums over generalist agencies, and OEMs pay willingly because the alternative — failed audits, delayed SOPs, safety recalls — costs orders of magnitude more.
The Sprint-Gate Collision
Here’s the failure mode we encounter most often when general agencies take on automotive software projects: they apply their standard two-week sprint cadence to a V-model engagement.
It collapses within the first quarter.
A system-level FMEA can’t be completed in a single sprint. A formal safety analysis review requires cross-functional sign-off from safety engineers, systems architects, and the OEM’s own safety team — that coordination alone takes weeks. Traceability matrix updates between requirements, design, implementation, and test artifacts aren’t a task you squeeze into sprint planning. They’re a continuous process obligation under ASPICE SWE.4 and SWE.5.
What happens mid-project is depressingly predictable: safety reviews get deferred to “the next sprint,” compliance documentation accumulates as technical debt, and the OEM review timeline — which was fixed from day one — starts slipping. By the time the team realizes they can’t sprint their way through gate reviews, they’ve burned three to four months of budget on deliverables that won’t survive an audit. For teams navigating this tension between agile and structured process models, understanding where each approach applies is non-negotiable before the project starts.
The Design-Engineering Gap
Can a single partner deliver both safety-critical embedded rigor and modern product design? In our experience, almost never — and that’s the sourcing problem nobody talks about in 2026.
Most automotive software vendors operate at depth in one domain or the other. You’ll find embedded specialists with deep AUTOSAR and ISO 26262 expertise who produce functional but visually dated HMIs. And you’ll find product design agencies that build gorgeous interfaces with no concept of how to integrate them with CAN bus data or comply with driver distraction guidelines like NHTSA’s visual-manual interaction limits.
The convergence point — where infotainment HMI design meets cloud-connected service architecture — is where this gap becomes a real project risk. Connected vehicle platforms need both: pixel-perfect UI built on genuine user research, and backend services that interface with vehicle diagnostics, OTA update managers, and telematics gateways.
MyPlanet Design — In-house teams covering UI/UX-intensive product layers alongside technically rigorous backend integrations, positioned for automotive projects combining HMI design with cloud-connected service architecture.
The lesson we’ve taken from watching this gap play out: don’t assume a vendor’s capabilities based on their portfolio vertical. Ask to see the specific team composition for your project. If the safety engineer and the UX designer have never worked on the same delivery before, you’re the integration test — and that’s not a risk worth absorbing in a domain where certification timelines don’t bend.
How Automotive Software Projects Fail — and the Warning Signs That Predict It

Most automotive software projects don’t fail because the engineering was poor. They fail because safety engineering was treated as a downstream concern — scoped after architecture decisions were already locked, and budgeted as if compliance were an afterthought.
The Budget Blindspot Nobody Quotes
Across more than five automotive engagements at ASIL-C and above, we’ve observed a consistent pattern: safety documentation — the safety plan, HARA, FMEA, FTA, safety case, and design verification methods — consumed 35–45% of total project budget. Every single time, the client was stunned. Their vendor had quoted development hours only, treating safety artifacts as minor overhead.
This is what happens when safety planning gets deferred past the concept phase. Architectural decisions made without safety constraints bake in structural rework that no amount of patching resolves. By the time a supplier realizes the safety plan conflicts with the existing architecture, the project is already months deep.
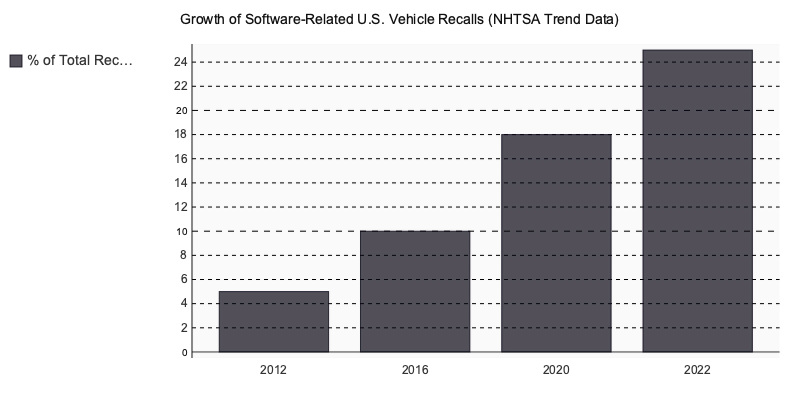
The commercial stakes are severe. According to NHTSA recall data, software-related vehicle recalls grew from under 5% of total U.S. recalls in 2012 to over 25% by 2022 — a fivefold increase in a single decade. Choosing underqualified automotive software development services isn’t just a project risk. It’s a recall liability.
Three Red Flags in Vendor Proposals
How do you catch these failures before they happen? Scan every proposal for three warning signs:
- No named Functional Safety Manager — ISO 26262 defines this as a mandatory process role, not a seniority title assigned retroactively. If the proposed team structure doesn’t include one, the vendor hasn’t staffed for safety.
- ISO 26262 listed as “familiarity” — without documented safety cases referencing specific ASIL assignments from completed projects, familiarity means they’ve read the standard, not applied it under audit scrutiny.
- No HARA methodology described — Hazard Analysis and Risk Assessment anchors every safety case. A proposal that omits it hasn’t planned past the demo phase.
The Prototype Trap
Here’s where budgets explode. Vendors build working demos — functional, polished, stakeholder-ready — without MISRA-C compliance, AUTOSAR integration, or real-time OS constraints. That code cannot be safety-certified.
Retrofitting ASIL compliance onto non-compliant code typically costs 3–5× the original development effort, a ratio consistent with published safety engineering case studies across the automotive technology domain. We’ve watched teams spend six months rebuilding what took two months to demo. The demo looked like progress. It was technical debt bolted to a steering wheel.
A Practical Checklist for Evaluating Automotive Software Development Proposals

Every vendor proposal should survive seven binary checks before it makes your shortlist. Each criterion is verifiable through project documentation — pass or fail, no partial credit, no “we’ll sort it out during onboarding.” If a vendor can’t produce these artifacts during the proposal phase, they won’t produce them under delivery pressure.
- ISO 26262 case studies naming a specific ASIL level and project type, available on request
- ASPICE assessment report issued by an independent third-party assessor — not self-declared
- Named Functional Safety Manager identified in the proposal by name, not “TBD”
- Tool qualification plan documented for every safety-critical toolchain element
- ISO/SAE 21434 TARA process demonstrated through a concrete past project example
- AUTOSAR Classic or Adaptive experience citing a specific named project reference
- DIA template shared before contract signature
Scoring Threshold
Three or more failures disqualifies a vendor — regardless of portfolio quality or pricing position. This isn’t an arbitrary cutoff. According to McKinsey’s research on automotive software programs, insufficient supplier qualification drives over 60% of project cost overruns (McKinsey & Company, 2024). We’ve watched vendors pass every commercial checkpoint only to fail the first gate review because nobody requested a DIA upfront. The OEM audit failure patterns covered in the previous section trace directly to these technical gates.
Where a vendor lands on this checklist correlates with engagement tier:
| Plan | Price Range | Features | Best For |
|---|---|---|---|
| Tier 1 Automotive Specialist | €€€€ | ASPICE L3+, ISO 26262 ASIL-D, AUTOSAR Classic/Adaptive, dedicated FSM team | Safety-critical ECU, powertrain control |
| Full-Stack Digital Partner (e.g., A dedicated platform) | €€–€€€ | ASPICE L2, ISO 26262 ASIL-B/C, modern CI/CD, UX-driven HMI | Connected vehicle apps, digital cockpit, HMI |
| General Software Agency | €–€€ | Standard SDLC, no automotive certifications | Non-safety companion apps, infotainment UI |
The most effective automotive software development services partners combine structured functional safety methodology with modern product development depth — identifying teams that hold both capabilities at the outset removes the compliance retrofit risk that derails the majority of automotive engagements.
Choosing the Right Automotive Software Partner Comes Down to Evidence, Not Promises
The difference between a successful automotive software engagement and a twelve-month rework cycle is almost always visible before the contract is signed. Vendors who can produce ASPICE assessment reports, name their Functional Safety Manager, and walk you through a completed safety case from a prior ASIL-C project aren’t hiding behind NDAs — they’re showing receipts.
Software development services demand a different operating model than general enterprise delivery. The toolchains are specialized, the compliance burden is front-loaded, and safety documentation will consume a third or more of your budget whether you plan for it or not. Accepting that reality during vendor selection — not during the first OEM audit — is what separates programs that ship from programs that stall.
Run every proposal through the seven-point checklist. Verify credentials independently. And if your current shortlist doesn’t include partners with proven AUTOSAR and ISO 26262 delivery experience, teams like A purpose-built tool are worth a conversation.
Written by Nazar Verhun, CEO & Lead Designer at MyPlanet Design.
Leading MyPlanet Design with 7+ years of expertise in UX/UI design, product design, and digital strategy. Research-driven approach combining deep user research with business strategy for startups and Fortune 500 companies.
Frequently Asked Questions
What is included in automotive software development services?
Automotive software development services typically cover five core areas: embedded ECU software built on AUTOSAR platforms, ADAS and sensor fusion pipelines for autonomous driving, connected vehicle and infotainment systems, diagnostic and testing tools, and functional safety engineering aligned with ISO 26262. Each domain requires specialized toolchains, compliance frameworks, and engineering expertise.
What is ASPICE and why does it matter for automotive software vendors?
ASPICE (Automotive SPICE) is a process assessment model used by OEMs to evaluate whether a software supplier follows mature, traceable engineering practices. Vendors typically need to demonstrate at least ASPICE Level 2 capability to qualify for automotive projects, as it proves they can produce consistent, auditable work products across requirements, design, coding, and testing.
How to choose an automotive software development partner?
Focus on verifiable process maturity rather than portfolio showcases. Key criteria include documented ASPICE Level 2+ assessment history, a proven traceability toolchain linking requirements to code to tests, ISO 26262 ASIL capability matching your product’s safety level, and a track record of passing OEM-specific audits — not just a list of client logos.
What is the difference between ASPICE 4.0 and ASPICE 3.1?
ASPICE 4.0 is an updated process assessment model that reshapes how assessors evaluate software engineering practices across the automotive supply chain. Compared to the legacy 3.1 framework, it introduces stricter requirements for traceability, process evidence, and engineering rigor, making it the recommended baseline for any supplier evaluation conducted from 2025 onward.
Why do general software companies fail automotive OEM audits?
Most failures occur because teams assume their existing quality management systems transfer directly to automotive standards — they do not. General software companies often pass technical interviews but cannot produce the traceable work products, safety documentation, and process evidence that ISO 26262 and ASPICE assessments demand, leading to costly disqualification during supplier audits.
What ASIL level does an automotive software vendor need to support?
The required ASIL (Automotive Safety Integrity Level) depends on your specific product’s risk classification, ranging from ASIL-A for low-risk functions to ASIL-D for the most safety-critical systems like braking and steering. Not every vendor is equipped to handle ASIL-C or ASIL-D projects, so it is essential to confirm their certified capability matches your product’s exact safety requirements before engagement.








