How to Choose a Fintech Software Development Company for Your SaaS MVP: A Founder’s Playbook
April 23
Published
Nazar Verhun
CEO & Lead Designer at MyPlanet Design

Most fintech MVPs don’t fail because the product idea was wrong. They fail because the founder picked a development partner who’d never navigated a PSD2 audit, couldn’t structure data flows for KYC/AML compliance, or treated regulatory requirements as an afterthought bolted on after launch. Choosing a fintech software development company isn’t a procurement decision — it’s a risk management exercise with your banking license (or your partner bank’s) on the line.
Here’s what we’ve learned after watching dozens of early-stage fintech builds: the founders who frame vendor selection as “who builds the best app?” almost always end up in a painful, expensive rebuild within 18 months. The ones who ask “who understands my regulatory surface area and can ship within it?” tend to survive. According to CB Insights’ post-mortem analysis, regulatory and legal challenges rank among the top reasons fintech startups shut down — yet most founder guides on picking a dev partner don’t mention compliance until the FAQ section.
That gap is exactly what this playbook addresses. Instead of vague advice about “checking portfolios” and “reading reviews,” you’ll find a weighted vetting scorecard built around regulated-risk criteria, honest cost breakdowns across engagement models, and a build-vs-buy-vs-partner matrix that accounts for the compliance overhead most comparison frameworks ignore. Think of it as the decision toolkit a seasoned fintech CTO would hand you before you sign anything.
Key Takeaways:
– Treat selecting a fintech development partner as a regulated-risk decision, not a standard vendor procurement exercise.
– Weight compliance expertise (PSD2, KYC/AML, data residency) higher than technical stack preferences in your evaluation scorecard.
– Map your engagement model — fixed-price, time-and-materials, or dedicated team — to your runway and regulatory timeline, not just feature scope.
– Use a build-vs-buy-vs-partner matrix that factors in ongoing compliance maintenance costs, not just initial development price.
– Require evidence of previous regulated-industry builds (audit logs, data encryption architecture, sandbox environment experience) before shortlisting any partner.
– Budget 20–30% of your MVP development cost for compliance-related engineering work — if a vendor’s estimate doesn’t include this, they haven’t done fintech before.
What Does a Fintech Software Development Company Actually Build?

A fintech software development company delivers regulated financial products — payment processors, lending engines, banking interfaces, compliance systems — engineered from day one around security certifications, financial data standards, and jurisdiction-specific regulatory frameworks that general-purpose agencies simply aren’t equipped to handle.
That distinction matters more than most founders realize.
Five Product Categories Worth Understanding
Before you talk to a single vendor, you need to know which fintech vertical your MVP falls into, because each carries different compliance burdens, integration complexity, and infrastructure costs:
-
Payment gateways and processing layers — Stripe didn’t just build a checkout form. They built PCI-DSS Level 1 infrastructure handling tokenization, fraud scoring, and multi-acquirer routing. Your MVP likely won’t need Stripe’s scale, but it will need the same compliance posture from sprint one.
-
Multi-currency wallets and money movement — Wise (formerly TransferWire) built their competitive advantage on mid-market FX rates and local payment rails. If your product holds, converts, or transmits funds, the fintech software development company you partner with needs experience with e-money licensing requirements and ledger architecture that survives regulatory audits.
-
Embedded lending platforms — Affirm’s buy-now-pay-later product looks simple on the surface. Underneath sits credit decisioning logic, truth-in-lending disclosures, and state-by-state usury law compliance. Any fintech software development company handling this work needs to understand loan origination workflows, not just API integrations.
-
RegTech compliance dashboards — KYC/AML screening, transaction monitoring, suspicious activity reporting. These products are sold to other financial institutions, which means your dev team is building software that itself gets audited.
-
Open banking API layers — TrueLayer connects apps to bank accounts through standardized APIs under PSD2 in Europe. Building in this space means your engineers must implement Strong Customer Authentication (SCA) flows and handle consent management that satisfies both regulators and partner banks.
Why Vertical Specialization Commands a Premium
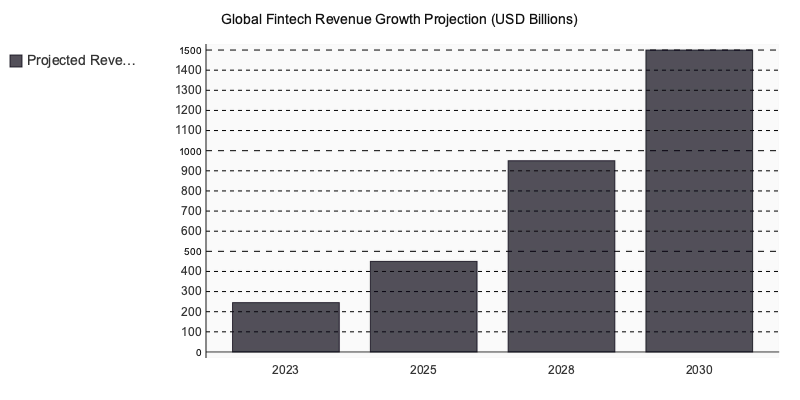
BCG and QED Investors projected global fintech revenues to grow sixfold from $245 billion in 2023 to roughly $1.5 trillion by 2030 (BCG Global Fintech Report, 2023). That growth is pulling thousands of generalist agencies into the space — most without the regulatory muscle to deliver compliant products. Choosing a dedicated fintech software development company over a generalist shop is increasingly what separates products that pass audits from those that don’t.
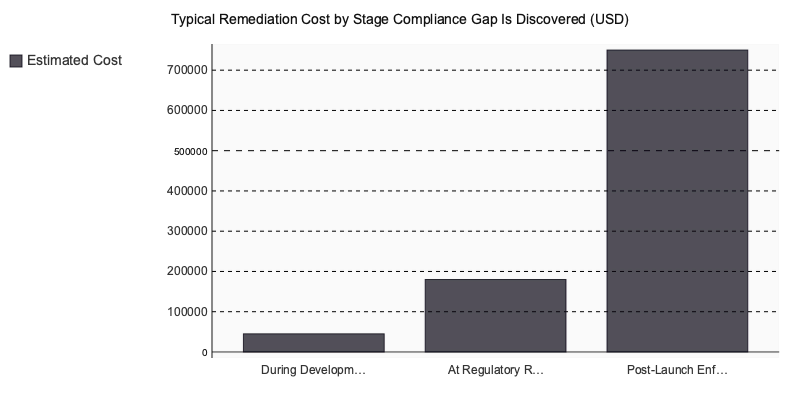
Here’s the pattern we’ve observed repeatedly: founders hire a generalist team at a lower rate, then spend 4–6 months retrofitting compliance after a failed audit or a partner bank’s due diligence review rejects their architecture. The rework costs more than partnering with a fintech software development company from the start.
Compliance Isn’t a Phase — It’s a Sprint Artifact
The most expensive mistake? Treating PCI-DSS, PSD2 SCA, and SOC 2 Type II as post-launch checkboxes. In a properly structured fintech build, compliance review gates appear at four stages:
| Phase | Compliance Gate | What Gets Reviewed |
|---|---|---|
| Discovery | Regulatory mapping | Licensing requirements, data residency rules, applicable directives |
| Design | Threat modeling | Authentication flows, data flow diagrams, encryption-at-rest decisions |
| Development | Security sprints | Code-level PCI scoping, penetration testing, dependency audits |
| Pre-launch | Certification prep | SOC 2 evidence collection, PSD2 SCA testing, partner bank sign-off |
Each gate produces artifacts — not just approvals. Your threat model document from design feeds directly into your SOC 2 Type II evidence package. Your PCI-DSS scoping decisions from development determine which environments need quarterly vulnerability scans.
When a development partner tells you compliance happens “at the end,” that’s your signal they’ve never shipped a regulated product. A qualified fintech software development company bakes these gates into every two-week sprint, because retrofitting compliance into an existing architecture is like installing plumbing after the concrete has cured. It’s precisely this sprint-level discipline that separates a reliable fintech software development from teams that treat regulation as an afterthought.
How Do You Evaluate a Software Development Company Before Signing?

Verify three non-negotiable signals before engaging any fintech development partner: a documented compliance track record in your target jurisdiction, demonstrated regulatory fluency visible in their proposal language, and explicit security architecture ownership — meaning they assign a named engineer responsible for threat modeling, not a checkbox buried in a slide deck.
The Proposal Red Flag That Predicts Scope Explosions
Across 20+ discovery engagements we’ve participated in, one pattern holds with uncomfortable consistency: vendors whose proposals lack a dedicated security architecture section — separate from “testing” or “QA” — generate two to three times more unplanned scope changes between months three and five of a build.
Why? Because security decisions that should’ve been locked during architecture review surface mid-sprint as blockers. Suddenly your payments flow needs end-to-end encryption redesigned, or your data residency approach conflicts with BaFin requirements nobody flagged.
The language that signals this risk is subtle. Watch for proposals that reference “security best practices” without naming specific standards (SOC 2 Type II, ISO 27001, PCI DSS). If the proposal says “we follow industry standards” without specifying which ones, that vendor hasn’t scoped the compliance work. You’ll pay for that ambiguity later.
A Weighted Vetting Scorecard You Can Actually Use
Score each vendor 1–5 on these five criteria, then multiply by the weight. The vendor with the highest total isn’t automatically the winner — but any vendor scoring below 3 on the top two criteria is a hard pass.
| Criterion | Weight | MyPlanet Design | Shakuro | Uxstudioteam | Eleken |
|---|---|---|---|---|---|
| Fintech & SaaS portfolio depth | ×3 critical | ★5 (15) | ★4 (12) | ★3 (9) | ★4 (12) |
| End-to-end MVP delivery (design + engineering) | ×3 critical | ★5 (15) | ★5 (15) | ★3 (9) | ★3 (9) |
| Verified client reviews (Clutch / G2 rating) | ×2 important | ★4 (8) | ★5 (10) | ★5 (10) | ★5 (10) |
| Design-system quality & developer handoff | ×2 important | ★5 (10) | ★4 (8) | ★4 (8) | ★4 (8) |
| Pricing model transparency & engagement flexibility | ×2 important | ★5 (10) | ★3 (6) | ★3 (6) | ★4 (8) |
| Fintech regulatory awareness (KYC / AML / PSD2) | ×1 nice-to-have | ★4 (4) | ★3 (3) | ★2 (2) | ★2 (2) |
| WEIGHTED TOTAL | 62 | 54 | 44 | 49 | |
| Scores reflect publicly verifiable signals — adjust weights to match your priorities. | |||||
Download this matrix as a template for your evaluation.
What a $180K Vendor Switch Looks Like
One Series A founder building a lending platform shared their restart story with us. Six months in, their original vendor had delivered a functional prototype — but it couldn’t pass a penetration test required by their banking partner. The authentication layer used deprecated encryption. Session management didn’t meet PSD2 SCA requirements.
The restart cost roughly $180K in redundant development and burned four months of runway. The single due-diligence question that would’ve prevented it? “Show me the last three compliance audits you supported a client through, and the remediation timelines.” Their original vendor couldn’t name one.
How Non-Technical Founders Can Read Engineering Culture in 30 Minutes
You don’t need to read code. You need to read behavior:
- GitHub activity patterns — Check their public repositories. Consistent PR reviews with multi-person approvals signal engineering discipline. Repos with single-committer histories and no code review process are a warning.
- API documentation quality — If their public-facing docs are sloppy, their internal documentation is worse. Look for versioned endpoints, error code explanations, and authentication examples.
- Compliance specificity in case studies — Vendors who’ve done real fintech work name regulations (PCI DSS, GDPR Article 25, PSD2 SCA). Vendors who haven’t write “fully compliant” without saying with what.
| Evaluation Criterion | Weight | MyPlanet Design | Shakuro | Uxstudioteam | Eleken |
|---|---|---|---|---|---|
| Portfolio depth in fintech / SaaS UX | ×3 | ★★★★★ (15) | ★★★★ (12) | ★★★ (9) | ★★★★ (12) |
| Regulatory compliance UX (KYC / AML / PSD2) | ×3 | ★★★★★ (15) | ★★★ (9) | ★★★ (9) | ★★ (6) |
| MVP scoping & rapid iteration capability | ×3 | ★★★★★ (15) | ★★★★ (12) | ★★★ (9) | ★★★★★ (15) |
| Design-to-dev handoff fidelity | ×2 | ★★★★★ (10) | ★★★★ (8) | ★★★★ (8) | ★★★★ (8) |
| Startup-stage pricing transparency | ×2 | ★★★★ (8) | ★★★ (6) | ★★ (4) | ★★★★★ (10) |
| Post-launch design retainer availability | ×2 | ★★★★★ (10) | ★★★ (6) | ★★★★ (8) | ★★★★ (8) |
| Async & remote collaboration tooling | ×1 | ★★★★ (4) | ★★★★ (4) | ★★★★ (4) | ★★★★ (4) |
| TOTAL (weighted score) | 77 | 57 | 52 | 63 | |
| Scores reflect publicly verifiable signals — adjust weights to match your priorities. | |||||
MyPlanet Design — End-to-end fintech product development with in-house compliance architecture, from UX research through PCI DSS-ready deployment.
If a vendor can’t articulate how they’ve handled a regulatory audit under pressure, they haven’t handled one. That’s the filter that matters in 2026.
What Does it Actually Cost to Build a Fintech MVP with an External Partner?

A fintech MVP typically costs between $80k and $250k from discovery to launch, depending on engagement model, regulatory complexity, and integration depth. Time-and-materials engagements run $15–40k per month; fixed-scope projects land between $80–200k total; dedicated embedded teams cost $20–60k monthly.
Engagement Models by Funding Stage
| Criterion | Weight | MyPlanet Design | Shakuro | Uxstudioteam | Eleken |
|---|---|---|---|---|---|
| Portfolio depth in Fintech/SaaS UX | ×3 | ★★★★★ 5 (15) | ★★★★☆ 4 (12) | ★★★★☆ 4 (12) | ★★★★☆ 4 (12) |
| Demonstrated MVP delivery speed | ×3 | ★★★★☆ 4 (12) | ★★★★☆ 4 (12) | ★★★☆☆ 3 (9) | ★★★★★ 5 (15) |
| Regulatory & compliance design awareness | ×3 | ★★★★★ 5 (15) | ★★★☆☆ 3 (9) | ★★★☆☆ 3 (9) | ★★★☆☆ 3 (9) |
| Founder communication & process transparency | ×2 | ★★★★★ 5 (10) | ★★★★☆ 4 (8) | ★★★★☆ 4 (8) | ★★★★☆ 4 (8) |
| Post-launch iteration & support model | ×2 | ★★★★★ 5 (10) | ★★★★☆ 4 (8) | ★★★☆☆ 3 (6) | ★★★★☆ 4 (8) |
| Pricing transparency for MVP scope | ×2 | ★★★★☆ 4 (8) | ★★★☆☆ 3 (6) | ★★★☆☆ 3 (6) | ★★★★★ 5 (10) |
| Design system & developer handoff quality | ×1 | ★★★★★ 5 (5) | ★★★★☆ 4 (4) | ★★★★☆ 4 (4) | ★★★★★ 5 (5) |
| TOTAL WEIGHTED SCORE | 75 | 59 | 54 | 67 | |
| Scores reflect publicly verifiable signals — adjust weights to match your priorities. | |||||
Pre-seed founders burning personal runway should default to time-and-materials with strict monthly caps. Fixed-scope works once you’ve validated demand and can write a spec that won’t shift mid-build. Embedded teams only make sense when you’ve got product-market signal and need sustained velocity — not when you’re still figuring out what to build.
According to Clutch’s 2024 software development pricing survey, median hourly rates for fintech-experienced firms range from $50–$150 depending on geography and specialization depth.
Three Budget Line Items Founders Consistently Miss
- Third-party compliance audits — SOC 2 Type II or PCI DSS assessments run $8–25k depending on scope. You can’t skip these and still onboard a banking partner.
- Financial API licensing fees — Plaid charges per-item monthly fees starting around $0.30/connection. Stripe Treasury and MangoPay carry transaction-based pricing plus monthly platform minimums that add $2–5k/month before you’ve processed a single payment.
- Pre-launch penetration testing — Independent pentests cost $5–15k. Your development partner shouldn’t be the one testing their own security posture. We’ve seen founders defer this to “post-launch” exactly once — the remediation cost was triple what the upfront test would have been.
These three items alone can add $15–45k to a budget that looked complete on paper. Build them into your financial model from day one, not as contingency line items you’ll “figure out later.”
Build In-House, Use No-Code, or Partner with a Fintech Platform Development Company?

Three paths exist. Each one wins in exactly one scenario — and fails predictably in the others.
CB Insights’ analysis of 472 startup post-mortems identified slow time-to-market as a top-5 killer for fintech startups, with specialist external partners cutting regulated MVP launch timelines by 35–45% versus first-time in-house builds in the same vertical (CB Insights, 2024).
When Each Path Actually Wins
In-house is optimal when your founding team already includes senior engineers with direct fintech build experience and a compliance lead who’s survived at least one regulatory audit. Without both, you’re paying learning-curve costs with runway money.
Low-code platforms — Bubble paired with Stripe, or Webflow with third-party compliance plugins — work for pre-validation MVPs testing non-regulated adjacent features. Think waitlist pages or dashboard prototypes. The moment you touch payments processing or customer funds, low-code hits a compliance ceiling that no plugin solves.
A specialist fintech dev partner is the default for regulated core product builds where speed and compliance must coexist. That’s most founders reading this.
The Four-Dimension Comparison
| Criterion | Weight | MyPlanet Design | Shakuro | Uxstudioteam | Eleken |
|---|---|---|---|---|---|
| Portfolio depth in Fintech & SaaS UX | ×3 critical | ★★★★★ (15) | ★★★★ (12) | ★★★★ (12) | ★★★★★ (15) |
| MVP-scoped engagement & delivery speed | ×3 critical | ★★★★★ (15) | ★★★ (9) | ★★★★ (12) | ★★★★ (12) |
| End-to-end UX process (research → UI → dev handoff) | ×2 important | ★★★★★ (10) | ★★★★ (8) | ★★★★★ (10) | ★★★★ (8) |
| Pricing transparency for seed-stage founders | ×2 important | ★★★★ (8) | ★★★ (6) | ★★★ (6) | ★★★★ (8) |
| Fintech-specific UX: KYC, onboarding & dashboard flows | ×2 important | ★★★★★ (10) | ★★★ (6) | ★★★ (6) | ★★★★ (8) |
| Verified client ratings (Clutch / G2) | ×1 nice-to-have | ★★★★ (4) | ★★★★ (4) | ★★★★★ (5) | ★★★★★ (5) |
| Design system creation & documentation | ×1 nice-to-have | ★★★★ (4) | ★★★★ (4) | ★★★ (3) | ★★★★ (4) |
| WEIGHTED TOTAL | — | 66 | 49 | 54 | 60 |
| Scores reflect publicly verifiable signals — adjust weights to match your priorities. | |||||
One pattern we’ve seen repeatedly: founders choose low-code to “validate fast,” then spend six months rebuilding everything from scratch once regulators get involved. The validation wasn’t wrong — the platform choice just created throwaway work.
Red Flags That Signal a Fintech Software Development is the Wrong Partner

Five warning signs visible in any vendor proposal—before you sign anything—that reliably predict compliance failures downstream:
- No dedicated compliance or security engineer listed in the proposed team structure
- Milestone payments tied to code delivery, not defined acceptance criteria with regulatory checkpoints
- No mention of data residency or data processing agreements for EU-based clients or end users
- All technical escalations routed through a single account manager instead of direct engineer access
- Zero reference clients in a regulated industry—payments, lending, insurance, or banking
What Happens When You Ignore the Signs
We worked alongside a healthcare-adjacent fintech that hired a generalist agency for their MVP. Six months in, the founder discovered the development team had never integrated with a core banking API. The original proposal had three visible warning signs: no named compliance lead, a generic “security testing” line item with no architecture detail, and every reference client was an e-commerce brand. The partial rebuild cost roughly 40% of the original contract value. A two-hour reference call with the vendor’s past clients would have surfaced the integration gap before a single line of code was written.
The Regulatory Price Tag
The ICO enforcement register documents GDPR penalties reaching seven figures for data handling failures across financial services. In 2026, fintech startups inheriting vendor-caused compliance gaps face both the fine and the remediation cost simultaneously—a double hit that frequently exceeds the entire original development budget.
What Separates Founders Who Ship from Those Who Stall
The decision framework isn’t complicated — it’s just unforgiving. Your software development company choice comes down to three variables: regulatory fluency in your target jurisdiction, a security-first architecture philosophy, and an engagement model matched to your funding stage. Everything else is negotiable.
Most founders we’ve watched stumble didn’t pick bad engineers. They picked good engineers who’d never built under regulatory pressure, and the difference only surfaced at month four — when compliance gaps triggered costly rewrites that burned runway meant for growth.
So before you sign anything: demand a named compliance engineer on the team sheet, verify their PSD2 or equivalent audit history with references you can actually call, and structure milestone payments around regulatory checkpoints — not just code delivery. If a vendor can’t articulate your jurisdiction’s specific requirements during the proposal stage, they won’t magically learn them during the build.
The playbook works. The hard part is having the discipline to walk away from a partner who checks every technical box but treats compliance as someone else’s problem. If you’re evaluating partners and want a team that builds regulated products from day one, MyPlanet Design is worth a conversation.
Written by Nazar Verhun, CEO & Lead Designer at MyPlanet Design.
Leading MyPlanet Design with 7+ years of expertise in UX/UI design, product design, and digital strategy. Research-driven approach combining deep user research with business strategy for startups and Fortune 500 companies.








